Executive Events

Dragos - COMING SOON !
Dragos is a cybersecurity firm specializing in protecting critical industrial infrastructure (OT/ICS) from cyber threats. They provide the Dragos Platform for asset visibility and threat detection, deliver specialized threat intelligence (WorldView), and offer expert incident response services to safeguard manufacturing, energy, and utility operations

Aembit.io - COMING SOON !
Aembit.io is a cybersecurity company specializing in Workload Identity and Access Management (IAM), often described as a "Non-Human IAM" platform. It enables enterprises to securely manage, audit, and enforce access between AI agents, applications, and APIs across cloud, SaaS, and on-premise environments.
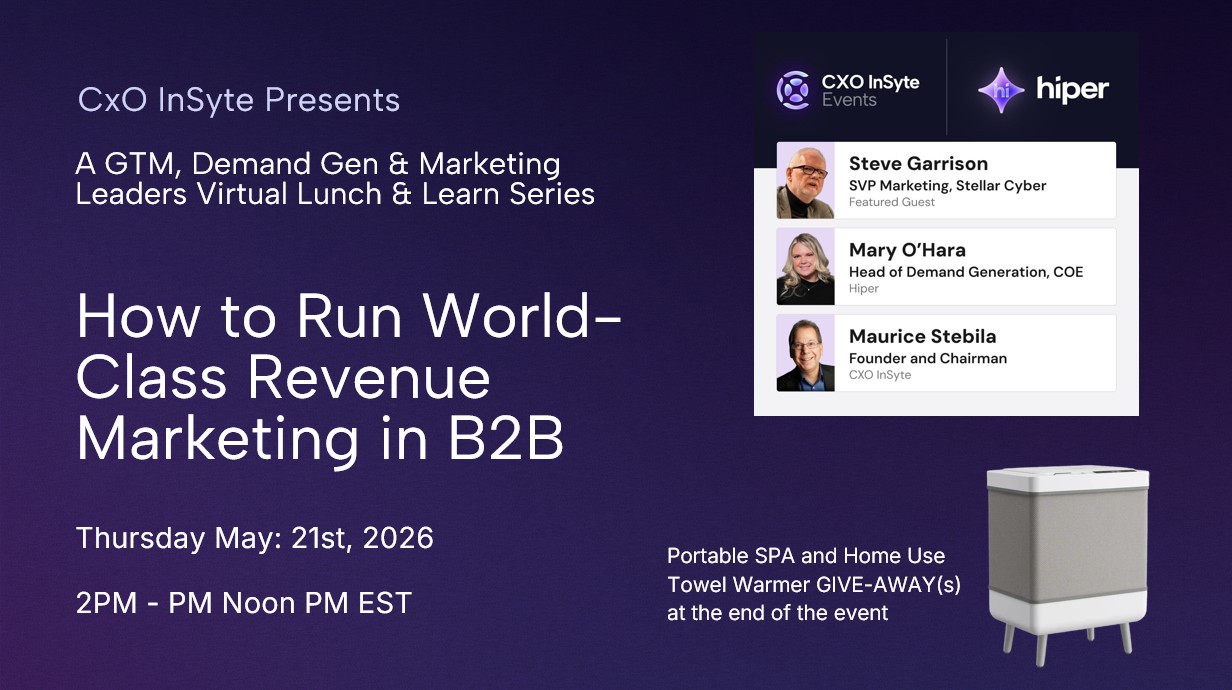
Running World-Class Revenue Marketing in B2B
Join a small group of senior marketing leaders for a live discussion with Steve Garrison, SVP of Marketing at Stellar Cyber. Steve will share how his team is approaching key initiatives across demand generation, including website and messaging updates, event strategy and experiences like RSA, and how they’re using campaigns and programs to engage buyers across their journey.

Hidden Cybersecurity Misconfigurations are not out of Reach
Join our cybersecurity executives for an exclusive roundtable discussion hosted by Reach Security, where we’ll explore how hidden misconfigurations quietly introduce risk—even in mature security stacks—and why traditional approaches often fail to detect and remediate them in time. This session will examine how organizations can move beyond point-in-time visibility toward continuous validation, optimization, and enforcement—unlocking the full potential of their existing security investments while advancing their Zero Trust posture.
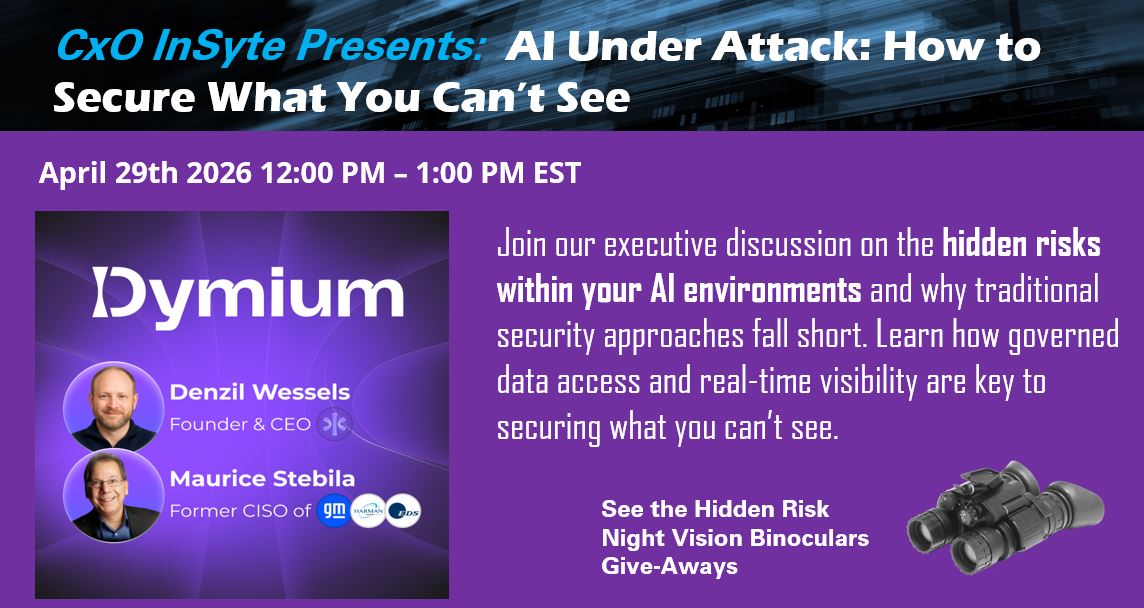
AI Under Attack: How to Secure What You Can’t See
Join our executive discussion on the hidden risks within your AI environments and why traditional security approaches fall short. Learn how governed data access and real-time visibility are key to securing what you can’t see. This session will explore how governed data access, real-time visibility, and modern security architectures are essential to protecting AI systems and ensuring trust at scale.

Alexander Steakhouse - Premier CISO Lunch Event at RSA
This peer-level Lunch & Learn discussion during RSA week will examine how Predictive Breach Prevention and AI-driven intelligence is helping organizations move beyond traditional detection toward proactively identifying and stopping threats before they become breaches.

[NEW ATTENDEES ONLY] ISC-WEST VIP CYBERSECURITY 4-DAY PASS
This Limited Offer is for NEW Cybersecurity Registrations that have not attended ISC West. Applicants will be reviewed to ensure a curated group of qualified security leaders. Approved attendees will receive a complimentary 4-day pass ($1,500 value) Email: eventrelations@cxoinsyte.events
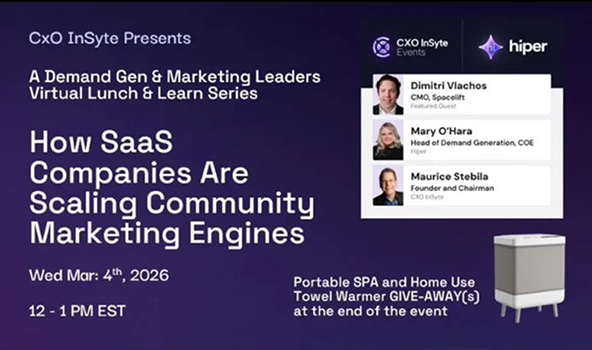
How SaaS Companies Are Scaling Community Marketing
Join your senior marketing peers and colleagues for a Lunch & Learn focused on how modern marketing leaders are building and scaling community marketing engines. CMOs and senior marketing leaders will trade ideas, best practices, and real-world examples of community-led strategies.

Future of Security: Cyber, Physical, Everything In Between
Join senior leaders and industry experts for a forward-looking conversation on The Future of Security: Cyber, Physical, and Everything In Between—and discover how the rapid convergence of cyber and physical security is reshaping risk, resilience, and protection strategies for modern enterprises.

How CMOs Are Driving More Demand-sourced Pipeline
Join your marketing colleagues as they share how they plan to drive more demand-sourced pipeline in 2026. CMOs and marketing leaders will trade ideas, best practices, and advice. Two guest speakers; a seasoned CMO to share how investments are shifting & a Demand Gen expert to share a playbook for growth marketing.
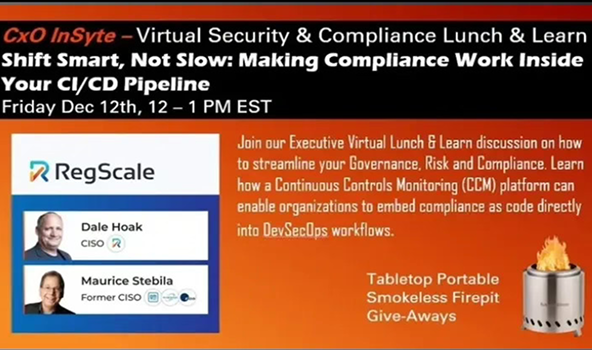
Streamline your Governance, Risk and Compliance.
Join RegScale for an executive Lunch & Learn discussion on how to streamline your Governance, Risk and Compliance. Learn how a Continuous Controls Monitoring (CCM) platform can enable organizations to embed compliance as code directly into DevSecOps workflows.
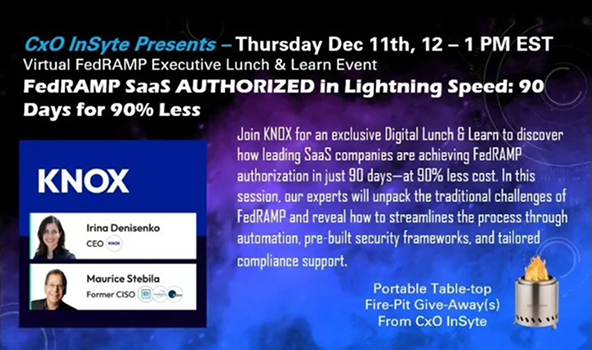
FedRAMP SaaS AUTHORIZED in Lightning Speed: 90 Days or Less
Join KNOX for an exclusive webinar to discover how leading SaaS companies are achieving FedRAMP authorization in just 90 days—at 90% less cost. In this session, our experts will unpack the traditional challenges of FedRAMP and reveal how to streamlines the process through automation, pre-built security frameworks.

FedRAMP SaaS AUTHORIZED in Lighting Speed: 90 Days or Less
Join KNOX for an exclusive webinar to discover how leading SaaS companies are achieving FedRAMP authorization in just 90 days—at 90% less cost. In this session, our experts will unpack the traditional challenges of FedRAMP and reveal how to streamlines the process through automation, pre-built security frameworks.
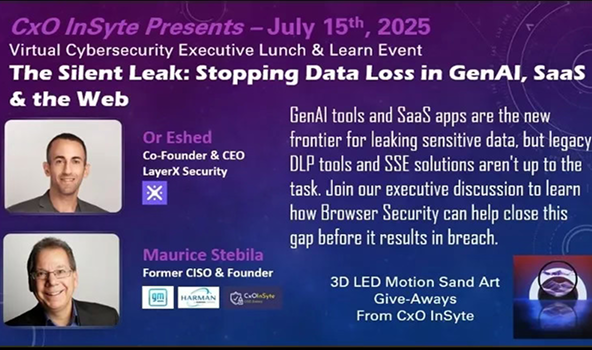
The Silent Leak: Stopping Data Loss in GenAI, SaaS & the Web
GenAI tools and SaaS apps are the new frontier for leaking sensitive data, but legacy DLP tools and SSE solutions aren't up to the task. Join our executive discussion to learn how Browser Security can help close this gap before it results in breach.
Partner With Us

